浦賀水道が目前に広がる温泉宿
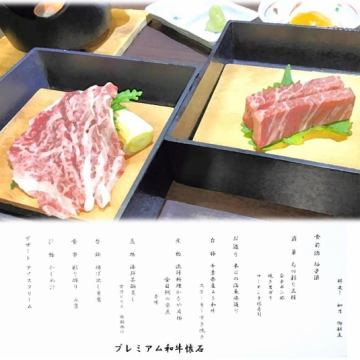
千葉県富津市金谷の『天然温泉 海辺の湯金谷』は、目の前に広がる内房の海、新鮮な漁師料理、茶褐色の天然温泉が自慢の宿です。
各部屋の壺風呂にゆっくり浸かり、日頃の疲れを癒しにお越しになりませんか。
隣のお食事処『漁師料理かなや』では新鮮なお魚料理のほか貝焼きをお楽しみ頂けます。
※現在貝焼きバイキングは休止してございます。セットか単品でご注文下さいませ。
各部屋の壺風呂にゆっくり浸かり、日頃の疲れを癒しにお越しになりませんか。
隣のお食事処『漁師料理かなや』では新鮮なお魚料理のほか貝焼きをお楽しみ頂けます。
※現在貝焼きバイキングは休止してございます。セットか単品でご注文下さいませ。